Camera Serial Numbers: What Are They All About?
A photo shows up online. Someone in the open source intelligence community checks the metadata and finds that the same camera serial number appears in another image posted earlier by a different account. That single data point is often enough to connect two accounts that were never meant to be linked.
The camera serial number is one of the more useful forensic identifiers embedded in image files. Every camera body, from a $15,000 flagship to a $600 Canon Rebel, is assigned a unique alphanumeric serial number. In most modern cameras, it is etched into a metal plate on the bottom of the body and hard-coded into the firmware.
When the camera fires, many models write this number into the MakerNotes section of the EXIF data. MakerNotes is a manufacturer-specific block that is not part of the core EXIF standard, so many generic metadata tools do not parse it at all.
The Forensic Clues in Every Image
When analysts have to investigate a photo, they do not just look at the pixels. Their job goes into the receipts attached to the image, aka the metadata. Even when it is missing, the core of the investigations revolves around figuring out:
- Time - When was the image taken?
- Place - Where was it taken?
- Device - What device captured it?
Each of these leads can be pursued independently and compared. The goal is to find out if they tell the same story. When inconsistencies emerge, the photo can be treated accordingly.
Serial numbers sit in the third category of device identification. However, the implications go much further.
The Stolen Camera Use Case
The serial number can be used to track a specific device across the web. Services like stolen-camera-finder and CameraTrace crawl sites such as Flickr, 500px, and public forums, indexing serial numbers found in EXIF data. Older uploads are often the most useful, since many platforms kept full metadata in earlier years.

Newer platforms are more aggressive about removing metadata, but historical archives might have what you are looking for.
If your camera is stolen, you can upload an old raw photo to the database. If the thief, or the unsuspecting person it was sold to, uploads a new photo taken with the camera, the system flags it.
From there, you have a GPS-tagged map leading straight to your stolen gear.
Of course, this only works if the metadata is not stripped, and it can be. If the image is reprocessed, screenshotted, or cleaned, the serial number will not be attached. In many modern workflows where processing is par for the course, this is exactly what happens.
Linking Anonymous Personas
The applications of this technology do not stop at trying to catch thieves. It can also be used in the world of journalism and counter-intelligence to link seemingly unrelated online personas.
Think of a scenario where a whistleblower leaks a photo of a sensitive document from a secure database. Six months later, a random travel blogger posts a picture of their vacation on Instagram.
If a forensic team finds the same serial number in both photos, the device itself links the two identities, assuming the metadata has not been altered. This is not foolproof. Cameras can be shared, borrowed, and resold. A matching serial number links images to a device, not necessarily to one person. When the data aligns with other evidence, it can still narrow the focus of an investigation significantly.
The Lightroom Edit History
This is one of those things guaranteed to make professional photographers sweat. When you edit an image in Adobe Lightroom or Photoshop, a log is created of what you are doing.
By default, when you export a JPEG, Lightroom can embed an XMP (Extensible Metadata Platform) block. If the "Include All Metadata" setting is checked, you will send the photo along with a step-by-step log of every aesthetic choice you made while using the software.
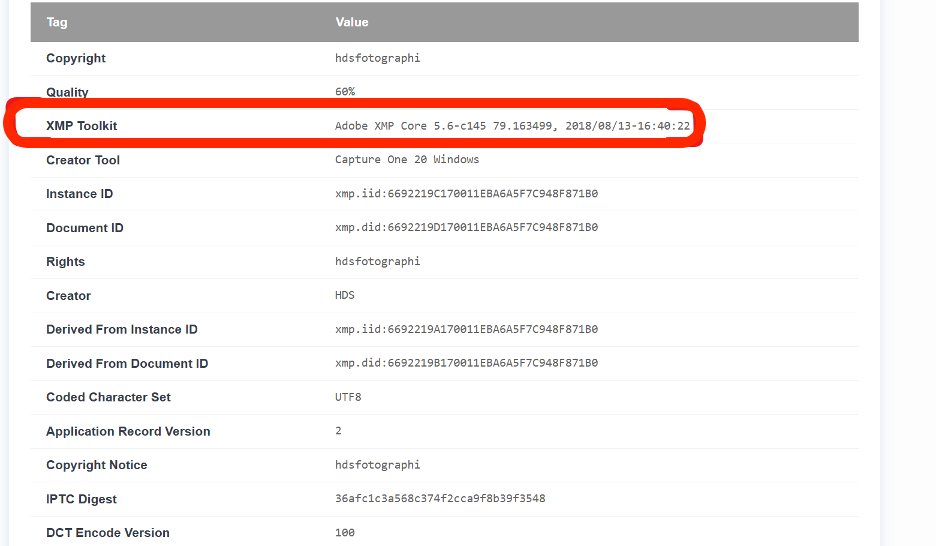
From this, an analyst can easily figure out if a photo was manipulated and exactly how. They can literally read the instructions, since the XMP data records:
- Exposure adjustment
- Brushing
- Cropping
- The order in which the edits were done...etc.
This kind of data is important to a journalist or investigator trying to maintain editorial or professional integrity. News editors can see, for instance, if a photo used in the news had its colors shifted to make a bruise look more violent, a sky more ominous, or other such edits.
Another thing that could happen is that photographers end up handing over their entire workflow. It is not uncommon for client-delivered JPEGs to have full edit histories, showing their presets, retouching techniques, and even mistakes that were not meant to be seen.
What Metadata Can and Cannot Settle
After analyzing thousands of digital footprints, forensic experts use a hierarchy of truth for metadata. It is a powerful tool, but it is not bulletproof. Here is what experts consider:
| The Question | Can Metadata Settle It? | What's The Limitation? |
|---|---|---|
| Chronology: Did this photo exist before the event? | YES | Metadata is excellent at proving a photo was taken before a certain date, making it a fraud detection mechanism. |
| Location: Was this taken at the scene of the incident/event? | PROBABLY | GPS tags are highly accurate, but can be spoofed or offset by a weak signal. |
| Device Linking:Did this camera take these three different photos? | YES | Serial numbers provide a nearly unbreakable link between different files. |
| Editing History:Has this image been edited in some way? | MOSTLY | Software tags and XMP logs record if a file was in Photoshop, but clever users can remove this data if they choose to. |
| Authorship: Whose finger was on the shutter button?? | NO | Metadata identifies the device, not the human. A camera can be borrowed, shared, or stolen. |
| Absolute Authenticity:Is this photo 100% real? | NO | Metadata is evidence, not proof. It can be faked with tools like ExifTool. In this use case, it needs contextual logic like weather, shadow consistency, etc., to come to any verdict. |
The pattern, as shown in this table, is consistent. Metadata is most useful when answering when, and with what, and weakest when answering who or why.
Metadata As Proof
In courtrooms or newsrooms, metadata is used as a "lead generator". If the EXIF data says a photo was taken in a blizzard, but pixels show a sunny day, you won't need forensic experience to suspect tampering.
However, if the metadata looks perfect, a good investigator may go for the secondary confirmation (such as Shadow Forensics) or the specifics of JPEG compression artifacts. In these professional settings, verification follows a process that can look something like this:
Metadata:
- What does the timestamp say?
- Does the location match?
- Does the device make sense for its specifications?
Context:
- Has this image been seen before?
- Is it recycled from an older event?
Consistency:
- Do multiple sources match with each other to tell a sensible story?
- Do the timestamps, devices, and location align with each other?
Metadata can be a witness, but it can be used to lie if the person behind the keyboard is skilled enough.
The best practice is to increase scrutiny when details start to drift and increase confidence if they align. Above all, expertise matters. There are many subtle clues an amateur might miss.
The Burden of Digital Proof
From journalists verifying sources to insurance adjusters inspecting a damaged car, metadata is often a useful starting point for establishing context. The serial number in particular is one of the more durable identifiers, but it only tells part of the story.
Metadata describes what a file claims about itself. It does not guarantee those claims are true.
